Windows Syslog Server and Compliance Software
Maximize your network security and implement compliance controls
Quickly identify and resolve security issues cost-effectively with Corner Bowl Server Manager, featuring both Linux and Windows syslog servers. When cost is an issue, Corner Bowl Server Manager is the leading choice for Information Systems Security Managers managing the vast security event log data generated by network hardware devices such as gateways, switches, firewalls and Linux servers. This enterprise solution simplifies syslog management, offering capabilities such as syslog consolidation, archiving, retention, real-time monitoring, reporting, and the implementation of compliance controls and inline auditing, ensuring a comprehensive and compliant approach to network security.
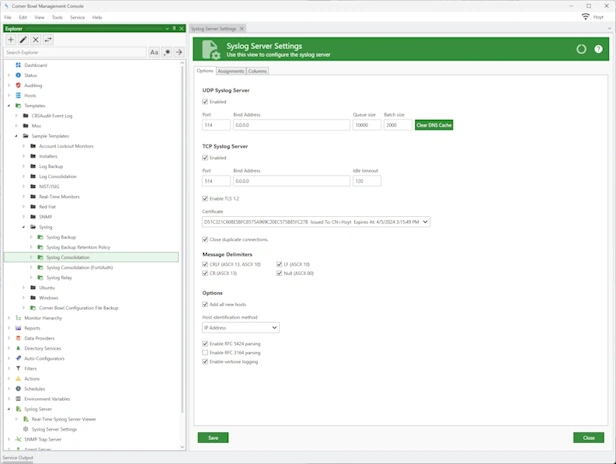
High Throughput Syslog Servers
- Runs on Windows, Red Hat and Ubuntu.
- Includes UDP, TCP and TCP with FIPS compliant TLS 1.2. encryption servers.
- Parses, filters and TCP server saves over 100,000 syslog messages per second.
- Bind to any port and Network Interface Card.
- Includes syslog relay support.
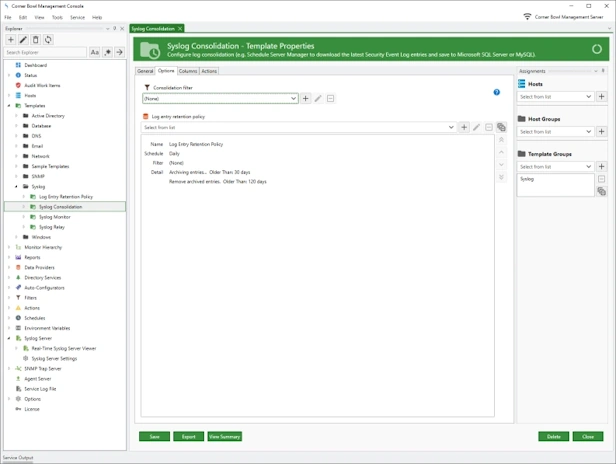
Syslog Consolidation and Backup
- Consolidate your syslogs by centrally saving and backing up your syslog messages to Microsoft SQL Server, MySQL, SQLite, text files or CSV files.
- Use regular expressions to parse attribute value pairs to their native data types then save to your RDBMS for internal and external analysis (e.g. integer, decimal and date/time).
- Use our Log Entry Retention Policy and Directory Cleaner Templates to automatically delete old syslog messages and file backups no longer required for compliance and auditing.
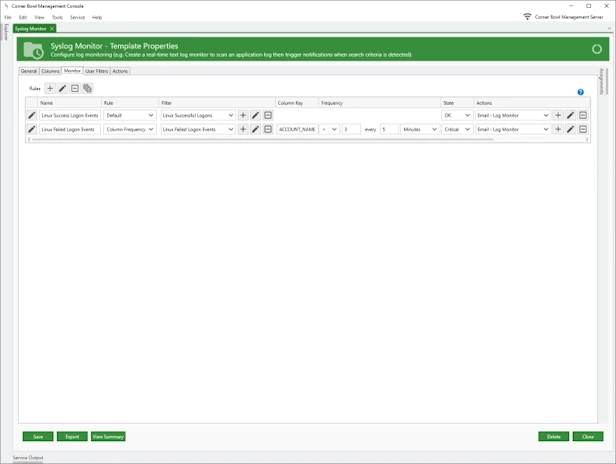
Syslog Monitor
- Real-time security auditing and monitoring for any hardware device.
- Automatically detect and apply IPS remediation actions, such as, running a PowerShell Command to block a IP actively involved in a cyber-attack.
- Parses RFC 5424 and RFC 3164 compliant messages.
- Use regular expressions to parse attribute value pairs to their native data types, for example, integer, decimal and date/time.
- Create Complex Filter Criteria to parse and filter any data typed attribute value pair.
- Apply correlation and frequency rules, for example, get notified when a task starts then completes, or a user fails to login 3 times within 5 minutes.
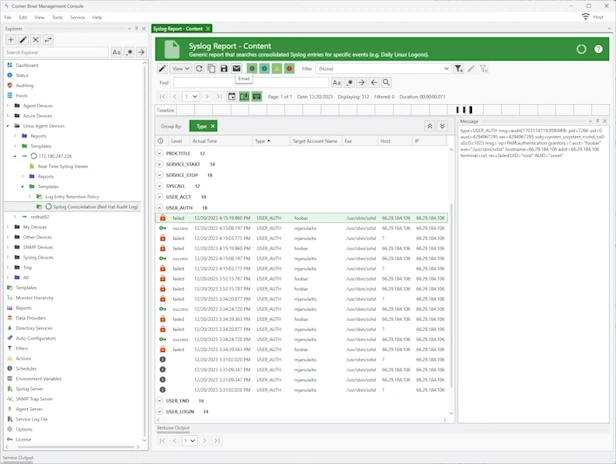
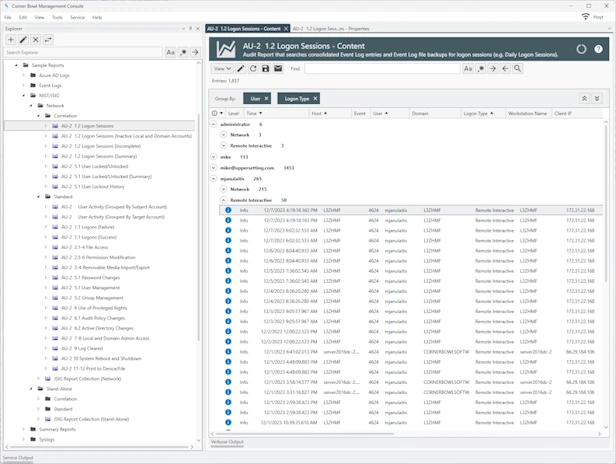
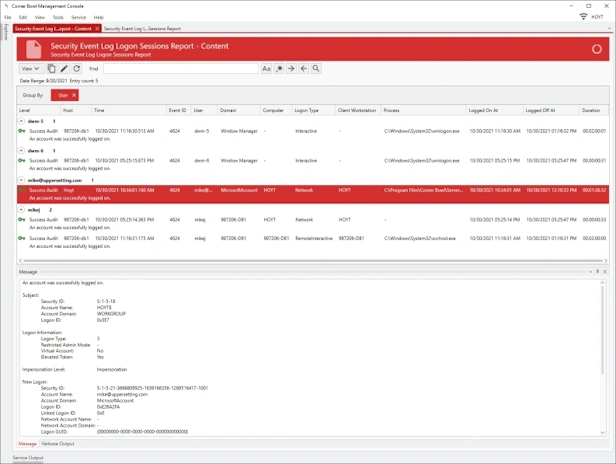
Syslog Reporting
- Generate security event reports to gain insight on events such as administrator logons, hardware device configuration changes and blocked packets.
- Customize report layout, event log entry columns, logos, colors, spacing and font sizes.
- Create and customize SIEM Reports that cross multiple log types, such as Windows Event Logs, Azure Entra ID Audit Logs, Red Hat Audit Logs and syslogs.
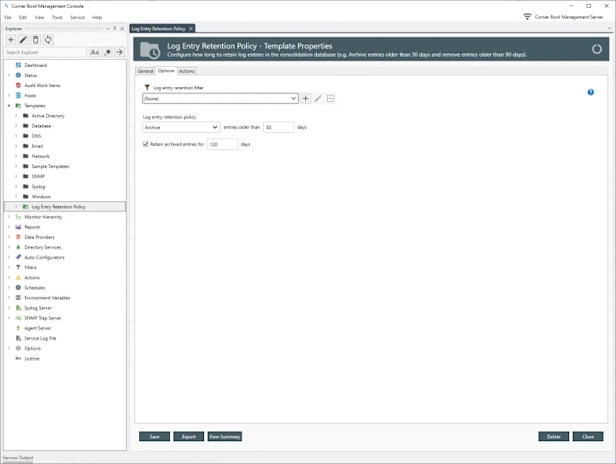
Syslog Retention Policy
- Configure how long to retain syslog messages in the log databases, for example, archive entries older than 30 days then remove archived entries older than 1 year.
- Schedule and manually remove syslog messages no longer required for analysis or compliance, for example, delete debug and informational syslog messages older than 90 days.
- Generate summary reports detailing the syslog retention metadata, for example, the data range and number of syslog messages in each syslog database table.
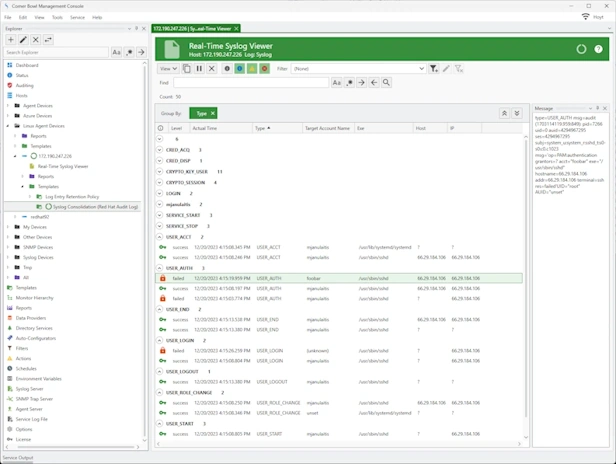
Syslog Analyzer
- Watch Syslogs in real-time.
- Page through large log files, search, highlight, view frequencies, mark entries and export result sets.
- Group and sort syslog messages using complex regular expression driven attribute value search criteria.
Syslog Message Correlation, IDS and IPS
- Group event syslog messages by column values then trigger alerts based on number of syslog messages in each group.
- Implement IDS and IPS remediation responses to active cyber-attacks.
Video Tutorials
Other Software Components
Related Links
Testimonials
Last Updated: December 6th, 2024