Intrusion Prevention System (IPS) Software
Detect and automatically neutralize cyber-attacks
Protect your network with our Intrusion Prevention System (IPS) software, a vital component against cyber-attacks. Our IPS offers real-time defense, proactively identifying and neutralizing risks before they harm your production environments. It's designed to detect and block active cyber-attacks and minimize downtime, making it an essential component of your cybersecurity strategy. With advanced threat detection, customizable intrusion detection policies, and comprehensive reporting, our IPS not only secures your network but also enhances its performance, offering peace of mind and cost-effective protection.
Intrusion Detection Systems (IDS)
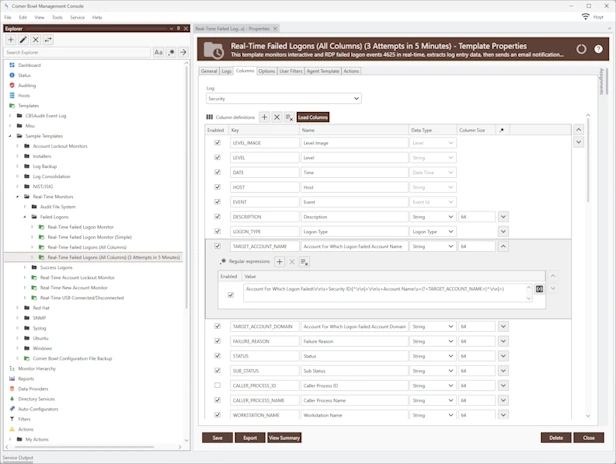
- Monitor Windows Security Event Logs, Azure Intra ID Audit Logs, Red Hat Audit Logs and Ubuntu Audit Logs to detect multiple consecutive failed logon attempts.
- Monitor IIS Web Server logs to detect phishing attacks.
- Monitor hardware device syslogs to detect firewall attacks.
Intrusion Prevention Systems (IPS)
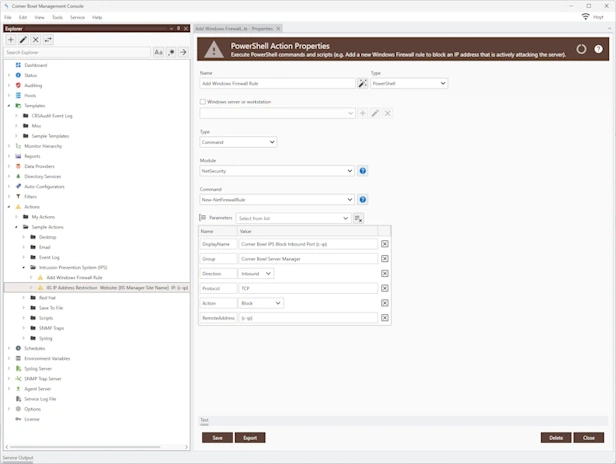
- Windows: Automatically block cyber-attacks by automatically adding Windows Firewall Rules to any managed Windows machine using our sample Agent-Based Windows Firewall PowerShell Action.
- Red Hat/Ubuntu: Automatically block cyber-attacks by automatically adding Linux Firewall Rules to any managed Linux machine using our Agent-Based Process Actions.
- IIS: Automatically block cyber-attacks by automatically adding IIS IP Restriction Rules to any managed IIS web server using our sample Agent-Based IIS IP Restriction Action.
Why do I need Intrusion Detection System and Intrusion Prevention System Software Tools?
Network security is paramount for organizations of all sizes. The ever-evolving nature of cyber-attacks demands robust and dynamic defense mechanisms. This is where Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) come into play, serving as critical components in safeguarding network infrastructure.
Intrusion Detection Systems (IDS)
Early Threat Detection:
IDS monitors network traffic and system activities for suspicious behavior, providing early detection of potential threats. This allows organizations to identify and assess unusual patterns or anomalies, such as unusual login attempts or unexpected data flows, before they escalate into full-blown attacks.Comprehensive Visibility:
IDS offers comprehensive visibility into the network, identifying not only external threats but also internal threats, which can often be more damaging. It keeps an eye on all network activity, ensuring that any malicious or anomalous behavior is quickly identified.Compliance and Regulations:
Many industries are governed by regulatory requirements that mandate the implementation of security measures like IDS. For instance, standards such as HIPAA for healthcare, PCI/DSS for credit card processing, and GDPR for data protection, often require IDS to ensure data security and privacy.Forensics and Analysis:
In the event of a breach, IDS provides valuable data for forensic analysis. It helps in understanding how the breach occurred and in identifying the vulnerabilities exploited, thereby facilitating improved security measures and policies to prevent future incidents.
Intrusion Prevention Systems (IPS)
Active Threat Prevention:
While IDS detects, IPS goes a step further by actively preventing and blocking identified threats. It functions as a control system that enforces security policies to prevent detected vulnerabilities from being exploited.Automated Response:
IPS can automatically take actions to prevent or mitigate a detected threat, such as blocking traffic from a suspicious IP address or terminating a harmful connection. This automation is crucial for immediate response, especially when dealing with high-speed networks where human intervention may be too slow.Enhanced Security Posture:
By integrating IPS, organizations can enhance their overall security posture. It acts as a second layer of defense, complementing traditional security measures like firewalls and antivirus software.Dynamic Threat Intelligence:
Modern IPS systems are often equipped with capabilities to update their threat intelligence dynamically. They learn from new threats and adapt their prevention mechanisms accordingly, offering protection against the most current and emerging threats.Business Continuity and Reputation Management:
By preventing interruptions caused by cyber-attacks, IPS helps in maintaining business continuity. It also plays a crucial role in preserving the organization's reputation by safeguarding against data breaches that can lead to loss of customer trust and potential legal implications.
Combining IDS and IPS for Optimal Protection
Integrating both IDS and IPS provides a comprehensive approach to network security. IDS serves as the early warning system, while IPS acts as the enforcer, actively blocking and mitigating threats. This layered security approach ensures that any malicious activity is not only detected but also promptly dealt with, providing a robust defense against the diverse range of cyber-attacks faced by organizations today. In summary, the implementation of IDS and IPS is not just a recommended practice but a critical necessity for protecting network infrastructure in the modern cyber landscape.
Other Software Components
Related Links
Video Tutorials
Testimonials
Last Updated: August 25th, 2024