Table of Contents
- Getting Started
- Agent-Based Management
- Common Tasks
- Data Providers
- Directory Services
- Auditing
- Hosts
- Templates
- Template Properties
- Batch Update Templates
- Assign Templates
- Log Management Templates
- SCAP Compliance Monitor
- Active Directory User Monitor Templates
- File and Directory Monitor Templates
- Windows Monitor Templates
- CPU Monitor Template
- Memory Monitor Template
- Disk Space Monitor Template
- Account Lockout Monitor Template
- Audit Policy Monitor Template
- Logon As Monitor Template
- Logon Monitor Template
- Performance Counter Monitor Template
- PowerShell Template
- Process Monitor Template
- RDP Session Monitor Template
- Registry Value Monitor Template
- Service Monitor Template
- SMART Disk Monitor Template
- System Security Monitor Template
- Windows Update Template
- WMI Query Template
- Task Scheduler Template
- Clock Synchronization Template
- Defragment NTFS Disks Template
- Network and Application Monitor Templates
- SSL Certificate Monitor Templates
- Database Templates
- Email Monitor Templates
- SNMP Monitor Templates
- Windows Accounts Templates
- Monitors
- Reports
- Auto-Configurators
- Filters
- Actions
- Schedules
- Environment Variables
- Options
- SNMP
- SSH Shell
- Syslog
- System Reset
- Shared Views
- Active Directory User and Group Filters
- Assign Actions
- Assign Azure Audit Logs
- Assign Consolidated Logs
- Assign Directories
- Assign Disks
- Assign Event Logs
- Assign Files
- Assign Services
- Assign Shares
- Auto-Config Host Assignment Properties
- Define CSV and W3C Log Entry Columns
- Define Log Entry Columns
- Define Log Entry Columns with Regular Expressions
- Executable Status
- Executable Timeline
- Explicitly Assigned Logs
- File Explorer
- General Executable Properties
- Report Columns
- Report Date/Time Ranges
- Report Security Event Log Filters
- Select Folder or File
- Target Files and Sub-Directories
- Command Line Interface
- Server Configuration
- Agent Configuration
- Troubleshooting
- Best Practices
- Terminology
Corner Bowl Server Manager
SIEM, IPS, Server Monitoring, Uptime Monitoring and Compliance Software
Duplicate Files Reports
The Duplicate Files Reports enable you to either manually on-demand scan any disk or directory then, using your own criteria, generate a report a report that lists duplicate files and optionally schedule the to be emailed to you or output to a file, for example, a CSV file.
Requirements
| Operating System | Technology |
|---|---|
| Windows | Remote WMI and Windows Shares |
| Linux | SFTP/SSH or FTP/S |
How to create a Duplicate Files Report:
- From the Menu Bar select File | New. The Create New Object View displays.
- From the Create New Object View, expand Report | File and Permissions Reports then select Duplicate Files Report. The Properties View displays.
Note
Unlicensed report types appear in gray text. If you would like to create a report that is not currently licensed, please contact Corner Bowl Software to upgrade your license.
- The Properties View contains 6 configuration tabs.
How to configure the Duplicate Files Report
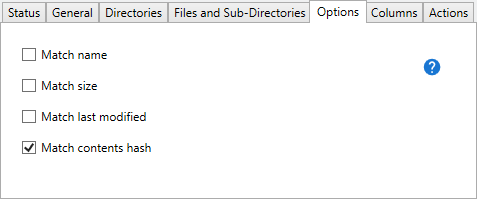
- Use the Match name check box to define a duplicate file when the names are the same.
- Use the Match size check box to define a duplicate file when the file sizes are the same.
- Use the Match last modified check box to define a duplicate file when the last modified date and times are the same.
- Use the Match contents hash check box to scan each file, generate a hash based on the file contents, then define duplicate files when the content hashes are the same.